Here after you will find step-by-step guide to deploy ADFS on Windows Server 2019.
Standard deployment topology
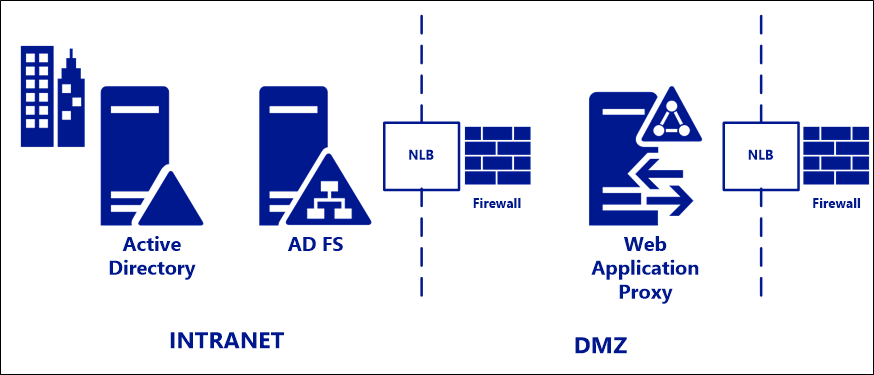
For deployment in on-premises environments, Microsoft recommend a standard deployment topology consisting of one or more AD FS servers on the internal corporate network, with one or more Web Application Proxy (WAP) servers in a DMZ or extranet network. At each layer, AD FS and WAP, a hardware or software load balancer is placed in front of the server farm and handles traffic routing. Firewalls are placed as required in front of the external IP address of the load balancer in front of each (FS and proxy) farm.
In my case, I will use a Citrix ADC in DMZ for Web Application Proxy.
Active Directory Federation Services (AD FS) also popularly known as SAML/Federation Services/SSO. It provides Web single-sign-on (SSO) to authenticate a user to multiple Web applications while utilizing a single account which makes end users life much easier at the time to login to their HR cloud-based app etc. ADFS also facilitates Azure AD Connect deployment for Office 365 and Azure deployments and integration.
ADFS 2019 had so many great features to facilitate and improve our deployments for more details see What’s new in Active Directory Federation Services for Windows Server 2019
ADFS Requirements
Here after is the details for my own lab:
- Federation Services DNS name
- Service Account or Group Managed Service Account (gMSA)
- Domain Admin Permissions
More info at Microsoft Docs : AD FS Requirements
Note: The following procedure is based on a fresh installed server domain-joined.
Installing Active Directory Federation Services (ADFS) Role on Windows Server 2019
To install utilizing PowerShell (Preferred/Easier method)

- Open PowerShell as administrator and run the following command

Installing via the Server Manager interface
- Open Server Manager console and click on Manage > Add Roles and Features

- Click on Next

- Click on Next

- Click on Next

- Select Active Directory Federation Services and click on Next

- Click on Next

- Click on Next

- Click on Install

- Click on Close

Configure ADFS Server Role
Note: Before we can configure ADFS we need to have a SSL Certificate for this server.
- Within Server Manager, navigate to the Flag icon click and select Configure the federation service on this server

- Ensure Create the first federation server in a federation server farm and is selected and click Next

- Click on Next

- Select SSL Certificate provide Federation Service Display Name and click Next

For more details see Microsoft, How to enroll an SSL Certificate for ADFS
- On the Specify Service Account page, you can either Create a Group Managed Service Account (gMSA) or Specify an existing Service or gMSA Account.

- In order to enable set the KDS Root Key, run the below PowerShell Command on a Domain Controller:
Add-KdsRootKey –EffectiveTime (Get-Date).AddHours(-10)

- Go back on the ADFS server, click Previous and Next

- Select Create a Group Managed Service Account, provide a name and click on Next

- Click on Next

Note: you could also specify a SQL Server, make sure you have a sysadmin or a least dbcreator permissions. For more details see Microsoft https://docs.microsoft.com/en-us/windows-server/identity/ad-fs/deployment/configure-a-federation-server.
If using a gMSA then you will need to pre-create gMSA Account via PowerShell:
$Name = 'adfs_gmsa'
$DNS_Name = 'adfs.arnaud.biz'
$PATRMP = 'biz-adfs-01$'
New-ADServiceAccount -Name $Name -DNSHostName $DNS_Name -PrincipalsAllowedToRetrieveManagedPassword $PATRMP

- Review options and click on Next

- Click on Configure

- Click on Close

- Restart your server after clicking on Close
Validation
Verify ADFS Services
- Open the Event Viewer and navigate to the ADFS View and search for the Event ID 100.

Verify that Federation Server is operational
- To verify that Internet Information Services (IIS) is configured correctly on the federation server, log on to a client computer that is located in the same forest as the federation server.
- Open a browser window, in the address bar type the federation server’s DNS host name, and then append /adfs/fs/federationserverservice.asmx to it for the new federation server, for example:https://biz-adfs-01.arnaud.biz/adfs/fs/federationserverservice.asmx
- Press ENTER, and then complete the next procedure on the federation server computer. If you see the message There is a problem with this website’s security certificate, click Continue to this website.

The expected output is a display of XML with the service description document. If this page appears, IIS on the federation server is operational and serving pages successfully.
Verify SSO
- Run the following PowerShell Command
Set-AdfsProperties -EnableIdPInitiatedSignonPage $true

- Browse to the ADFS sign-in page and test authentication. https://federationservicename/adfs/ls/idpinitiatedsignon

- Click on Sign In

- You should see a message standing that your are signed in

References
ADFS Deployment https://docs.microsoft.com/en-us/windows-server/identity/ad-fs/ad-fs-deployment
To follow
In a next article I will explain the configuration to provide external access to ADFS Server using Citrix ADC
